
Services > VPC > Launch VPC Wizard > Single public subnet.
Provide IPv4 CIDR block for the entire VPC. All resources within that VPC will assume IP addresses in the specified range. A typical range is [ 10.0.0.0/16 ]
Provide IPv4 CIDR block for the public subnet. A typical range for a single AZ subnet is [ 10.0.0.0/24 ].
Note: - If the public subnet is to be divided into 2 say for AZ a and b then a typical range for subnet A would be [10.0.0.0/25] and [10.0.0.128/25] for subnet B
Create a private subnet with CIDR [ 10.0.1.0/24 ] for single AZ subnet.
After VPC is created, it is not public yet. It doesnt know how to connect to the internet. So modify its route table to connect it to IGW (internet gateway).
Open VPC route table and Add a new route with destination 0.0.0.0/0 and Target to igw-guid. This is the default IGW provided by AWS.
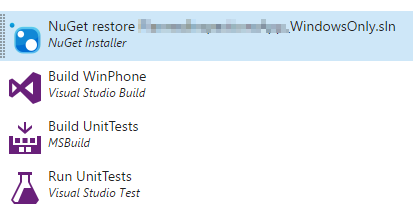 Building and Deploying apps using VSTS and HockeyApp - Part 3 : Windows Phone
Building and Deploying apps using VSTS and HockeyApp - Part 3 : Windows Phone
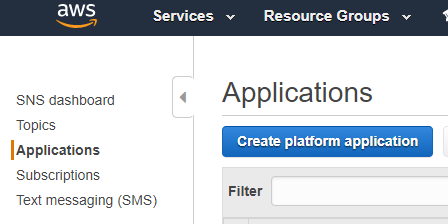 Apple Push Notifications With Amazon SNS
Apple Push Notifications With Amazon SNS